The public cloud infrastructure used to host the Scotland’s proximity contact tracing app has been configured so no one can access user data which is entirely anonymised and encrypted at source, the Scottish Government has insisted.
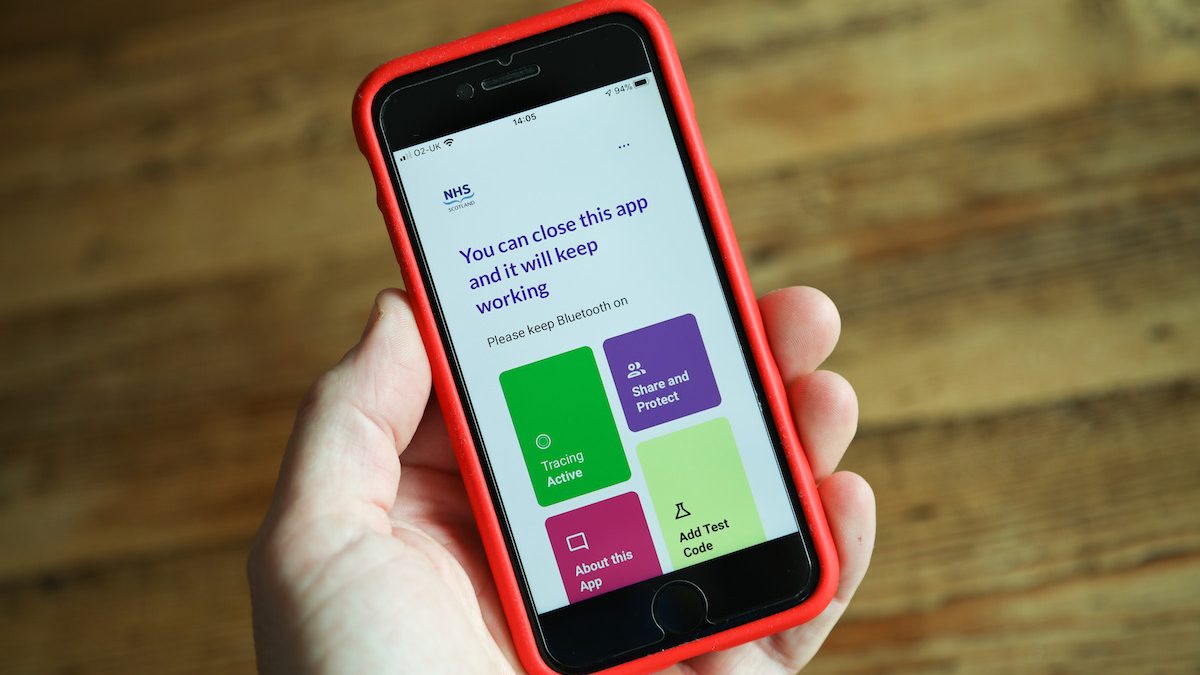
The NHS Scotland Protect Scotland app, which has now been downloaded by 1.1million people in Scotland, relies on a Bluetooth based ‘exposure notifications system’ developed by Apple and Google which cannot track a user’s location, nor see individuals’ identities.
Only the app itself, which sits on an Amazon Web Services cloud account owned by NHS Education for Scotland, can receive data, but because it is encrypted – turned into random numbers – it means it is entirely anonymised and cannot be associated with someone’s personal information.
A Scottish Government spokesperson said: “The Scottish Government takes the privacy of app users incredibly seriously. That is why a deliberate choice was made that Protect Scotland would use the privacy-first ‘decentralised’ Google/Apple Exposure Notification System, and why an ethical framework was adopted for the development of Protect Scotland. A number of privacy groups were engaged throughout the development of Protect Scotland, as were the Information Commissioners Office. A full Data Protection Impact Assessment has been published alongside a detailed explanation of how people’s data is used. In the interests of full transparency the Scottish Government has also made available the source code used to develop the Protect Scotland app.
“Whilst Amazon Web Services do process some data, as set out in the Privacy Notice and the DPIA, this is done using an existing NHS Education for Scotland (NES) cloud storage account provided by AWS. Only NES control access to this and the data stored in the app backend is entirely anonymised codes. It complies to all NHS Scotland and GDPR data standards, in the same way that all other data that is handled by NHS Scotland and its contracted providers does. Users’ mobile number, test code (and the relevant date) and IP address are not stored by the app and they are not made visible by the app to anyone, including AWS.”
Privacy fears were raised last week over disclaimers included in the download section of the app, which meant users had to automatically agree to Amazon Web Services accessing “personal information”. That information pertained to a mobile phone number, estimated date of infection, an authorisation code, the IP address, the exposure notification and confirmation of app use [which] will go to the NHS. However, the Scottish Government – which contracted the services of Irish company NearForm in developing the app, insisted all the information would be encoded and could not be read by AWS, or them.
Google and Apple have both published privacy notices which insist the exposure notification system – which uses a Bluetooth setting users must agree to switch on for the app to work – does not allow for people’s locations to be tracked, or their identities to be revealed. They say that the Bluetooth system instead only collects random ID numbers from others users who have the app installed, and ENS enabled on their smartphones, whether they be Android or Apple iPhone users. That system only swaps the IDs – described as a ‘virtual handshake between devices’ – if the people who have the setting switched on are within a two-metre proximity of someone else who has the app activated for 15 minutes or more. Anyone that tests positive for COVID-19 in Scotland will then be contacted by a contact tracer, who will ask them about their close contacts and whether they are an app user. If they are an app user, the contact tracer will send them an SMS message with a randomly generated test code to enter into their app alert.
The app will then seek permission to share the anonymous IDs it has been gathering from close contacts over the past 14 days. These IDs are stored on a secure NHS Scotland server so that other users’ apps can periodically check-in to see if they match up with a positive case.
The spokesperson added: “In NearForm and AWS, we are using trusted suppliers used by multiple governments, with all of our work complying with GDPR. We have also carried out a detailed security assessment, with advice from the UK National Cyber Security Centre.”
Scotland’s leading cryptographer, Professor Bill Buchanan, OBE, said: “As a society, we don’t quite understand how the public cloud works. I use AWS, but I own data infrastructure and I am responsible for the security (not Amazon). I can encrypt my data at the source, and Amazon will never see it. I can apply my own access controls on it, and Amazon will never be able to access the data. We really need to be talking about the cloud in a better way and – as experts – get involved in the debate, otherwise we will fail to build new cloud-based systems which better protect our citizens.”